Every second of 2024, an Australian experienced a cyber attack. Australia has secured the number 11 spot in the race of nations most affected by cyber attacks, after it suffered 47 million data breaches in 2024.
Behind these staggering numbers lie stories that should terrify every Australian business leader: Latitude Financial's breach cascading from 328,000 to 14 million affected records, Medibank's 9.7 million customer details stolen by Russian ransomware groups and countless smaller businesses discovering their "secure" systems were anything but.
The financial damage is equally sobering. Data breach cost Latitude $76 million – and that's just one company's price tag for inadequate data protection.
When 'it won't happen to us' becomes front-page news
The pattern emerging from Australia's biggest corporate breaches reveals uncomfortable truths about how businesses handle sensitive information. Take Latitude Financial's trajectory from confidence to crisis.
March 2023 timeline:
- Week 1: "Limited breach affecting 328,000 customers"
- Week 2: "14 million records were exposed, including passport numbers"
- Week 3: Cost projections soar beyond $76 million
What turned a manageable incident into a corporate nightmare? The same vulnerabilities are plaguing Australian businesses across every sector: over-reliance on legacy systems, insufficient employee access controls and critically – inadequate protection of sensitive document exchanges.
Expert Analysis: Cybersecurity experts described the Latitude breach as a "ridiculous" failure to mitigate the risk of data being handled by third-party service providers, highlighting systemic weaknesses in how Australian companies manage sensitive information during critical business processes.
The hidden vulnerability: Where deals die and data disappears
While headlines focus on customer data theft, a more insidious problem lurks in corporate boardrooms. Australian businesses routinely share their most sensitive information – financial records, acquisition plans, intellectual property – through platforms that wouldn't survive a determined attack.
Case Study Snapshot:
A Sydney-based mining company discovered during a $500 million acquisition that its chosen document-sharing platform stored files on overseas servers with no encryption. The deal collapsed when due diligence partners refused to proceed without adequate data protection guarantees.
This scenario repeats across industries. In December 2022, Medibank, the Australian health insurance giant, was the victim of a major data breach, affecting the personal details of 9.7 million customers – but the real damage extended to partner companies and vendors who had shared sensitive commercial information through compromised channels. For Medibank, the cost of failing to mitigate against the risk of a third party handing over high-level credentials to an attacker has already reached $26 million, though it expects that figure could be as high as $45 million by the end of the financial year.
The 2025 reality check: New threats, same old mistakes
Australian organisations are set to spend A$6.2bn on security and risk management in 2025, a 14.4% jump from the previous year, yet many continue making fundamental errors in data handling.
What's changed:
- AI-powered attacks targeting Australian businesses specifically;
- ransomware groups focusing on document repositories;
- cross-border compliance requirements tightening under updated Privacy Act; and
- ASIC demanding enhanced digital audit trails for public companies.
What hasn't changed:
- businesses treating document security as an IT problem, not a strategic imperative;
- over-reliance on consumer-grade file-sharing solutions for commercial transactions; and the
- assumption that encryption alone provides adequate protection.
Table: Cost Comparison of Security Approaches
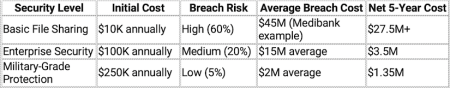
The mathematics are brutal: spending more on protection costs dramatically less than recovering from breaches.
Lessons learned the hard way
Australian businesses are finally absorbing painful lessons from recent cyber catastrophes. The smart money is shifting toward comprehensive data protection strategies that go beyond traditional IT security.
The new essentials:
End-to-end encryption:
Not just file storage, but the entire communication and sharing process. Due to the rise in credential stuffing-related data breaches, businesses need platforms where stolen passwords become useless.
Geographic data control:
Following the Medibank and Optus attacks, Australian businesses increasingly demand data sovereignty – knowing exactly where sensitive information is stored and who can access it.
Real-time monitoring:
The difference between Latitude's initial assessment (328,000 affected) and final reality (14 million) highlights why businesses need instant visibility into data access and sharing.
Compliance integration:
With OAIC ramping up enforcement and ASIC tightening requirements, data platforms must demonstrate regulatory compliance from day one, not as an afterthought.
Beyond basic security: The strategic advantage
Forward-thinking Australian companies discovered an unexpected benefit from investing in sophisticated data protection: competitive advantage in deal-making and partnerships.
Historical Perspective:
As former FBI director Robert Mueller noted: "There are only two types of companies: those that have been hacked, and those that will be." This reality has become particularly acute for Australian businesses, where companies using sophisticated data room providers in Australia are completing transactions faster than those relying on basic file-sharing solutions.
This trend reflects broader market recognition that data security isn't just risk management — it's a business enabler that can accelerate growth, partnerships, and investment opportunities.
Real-world impact:
- faster due diligence processes with international partners;
- higher confidence from institutional investors;
- reduced insurance premiums for cyber liability coverage; and
- enhanced reputation among security-conscious business partners.
What 2025 actually demands
The cybersecurity landscape facing Australian businesses has fundamentally shifted. 38% of all data breaches resulted from cybersecurity incidents, but the most sophisticated attacks now target the document and communication platforms businesses use for their most critical operations.
The question isn't whether your business will face a cyber threat – it's whether your data protection strategy can withstand the kind of determined attacks that brought down Latitude, Medibank, and dozens of other Australian companies.
The strategic framework:
- Assume breach: Design systems assuming perimeter security will fail
- Protect in transit: Focus on data security during sharing and collaboration
- Verify everything: Implement zero-trust principles for document access
- Plan for transparency: Ensure your security measures satisfy regulatory scrutiny
The businesses thriving in 2025 are those that learned from Australia's cyber catastrophes without experiencing them firsthand. They understand that in an environment where attacks occur every second, the only sustainable approach is making data protection so robust that breaches become operationally and financially irrelevant.
The $76 million question every Australian business leader must answer: Can you afford to learn these lessons the hard way, or will you implement military-grade data protection before your company becomes the next cautionary tale?